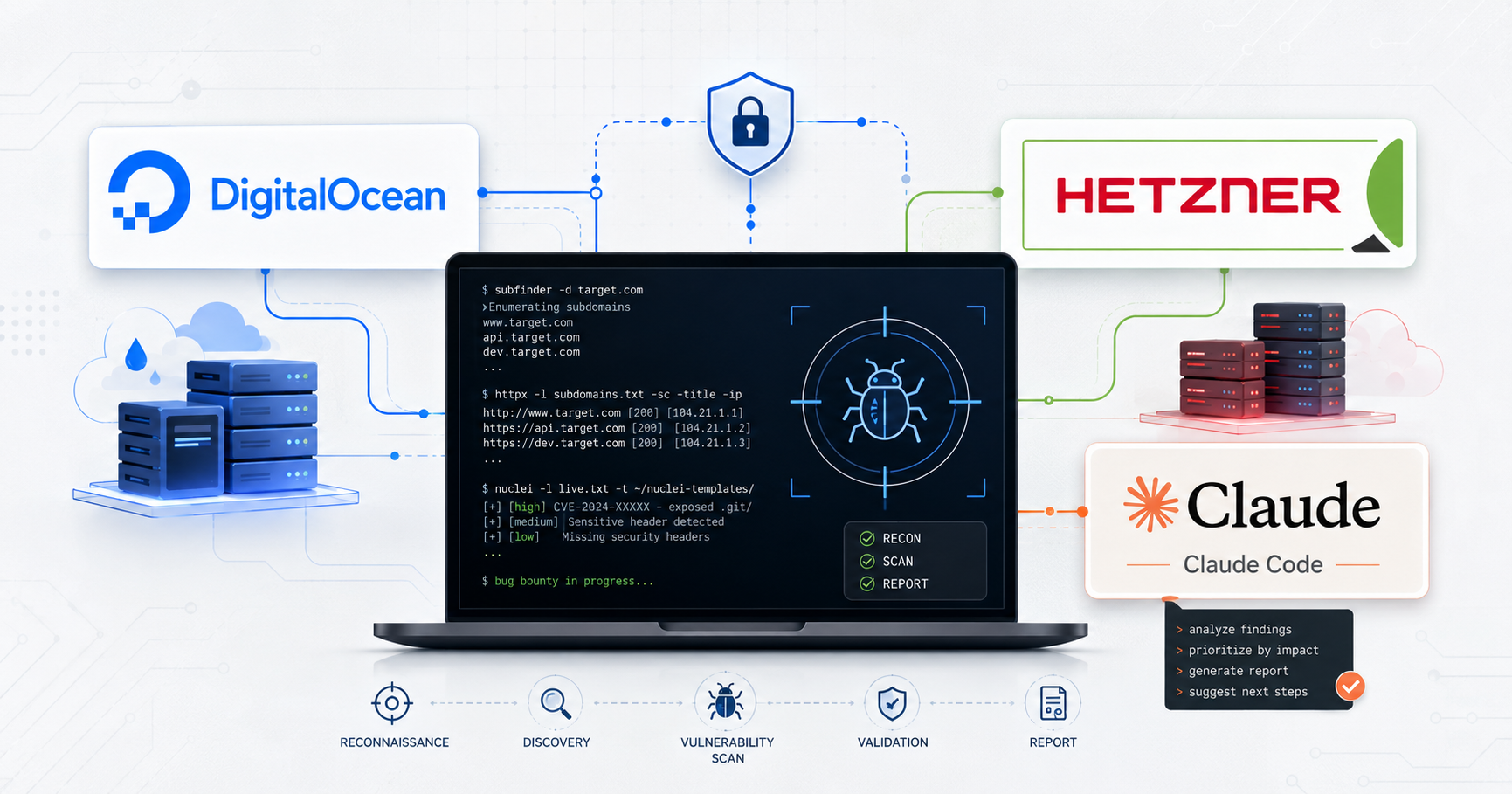
So you are getting serious about Bug Bounty then it’s time to get a serious setup. This means:
- VPS running 24/7 ready to kick off automation or run scheduled automation at a moments notice
- Recon via Fleet distribution
- Claude Code configured
- Leveraging modern tools
- SSH configured with
tmuxto pick up where you left off
Who this setup is for (and what it is not)
This post is designed to share how I’ve setup my environment and what has been working for me and what might work for others. This is NOT the keys to finding any and all vulnerabilities by launching a few nuclei/AI scans that will identify all criticals at once.
You do not need to invest money to find bugs but if you are serious about getting bounties then investing money into your environment will absolutely pay for itself.
VPS - Cloud Computing
The easiest place to start is to identify our cloud provider.
Before we dive into the logistics of cloud providers lets first talk about why
Pros
- IP Protection - you do not want your home IP to get blacklisted, trust me
- Remote work - Bug Bounty is about obsession, even on that nice vacation that itch to work might show up and you want to be able to pickup where you left off at any time
- Fleet provisioned work - Instead of running recon with 1 computer, why not spin up a fleet of 20
- SSRF/OOB attacks
- Speed (Download/Upload)
Cons
- Resource cost
- Limited RAM/Storage
- MCP integration with Burp Suite or local tools — still possible
There are many more but the pros absolutely outweigh the cons and I would consider this a necessity for serious hunters.
Which Provider?
Okay I’ve sold you on getting a VPS setup now which VPS provider should you go with? Options:
- DigitalOcean
- Hetzner
- AWS
- Linode
- Etc
We are going to focus on two primary hosts DigitalOcean and Hetzner. Originally I used DO but recently I’ve switched to Hetzner as it’s a no brainer. Hetzner gives you a lot more for less.
Let’s first think about what we need from our provider. For a main controller box, I’d start with at least 4 GB of RAM and 80 GB of disk. That gives you enough room for toolchains, wordlists, logs, scan output, and a few long-running tmux sessions without constantly fighting the machine.
| Provider / plan | Monthly price | CPU type | vCPU | RAM | Disk | Included transfer |
|---|---|---|---|---|---|---|
| DigitalOcean Basic Regular | $24.00 | Shared | 2 | 4 GB | 80 GB | 4 TB |
| Hetzner US CCX13 | $19.99 | Dedicated | 2 | 8 GB | 80 GB | 1-8 TB depending on location/tier |
| Hetzner EU CCX13 | $18.49 | Dedicated | 2 | 8 GB | 80 GB | 20 TB |
| Hetzner US CPX31 | $24.99 | Shared | 4 | 8 GB | 160 GB | Varies by US tier |
That’s right, for less than DigitalOcean you get twice the RAM and dedicated CPUs. I recommend using a CCX13 for your base server/controller. Go here to sign up Hetzner (no referral, just a great product)
Quality of Life
I won’t walk you through configuring your VPS however I highly recommend you create an ssh alias on your host machine to quickly connect to your VPS ensure you add your ssh pubkey to authorized_keys:
cat ~/.ssh/config
Host droplet
HostName <VPS IP>
User <username please don't use root>
IdentityFile ~/.ssh/droplet_key
IdentitiesOnly yes
# LocalForward 1234 127.0.0.1:1234 -- If you want to portforward for a service you have running on the VPS uncomment these fields.
# ExitOnForwardFailure yes
# ControlMaster auto
# ControlPath ~/.ssh/cm-%r@%h:%p
# ControlPersist 10m
Fleet provisioning: why Axiom (or any fleet tool) matters
Okay great, you have your VPS controller setup, next you will want to figure out what fleet provisioning tool you’ll want to use. I use Ax Framework this essentially allows you to use cloud resources to rapidly complete recon or scans. Axiom is quite easy to setup just follow the installation instructions. Use the easy install on the VPS. I will create a separate writeup on the recon pipeline I use.
Workflow: using Claude Code responsibly for ops tasks
Next thing you’ll want to setup is Claude Code, AI gets a bad rap but from a vulnerability hunting perspective it is an absolute game changer. I will have a blog post dedicated to how you can utilize AI optimally for identifying Bug Bounties or vulnerabilities in general. Stay tuned for that. For now get claude code installed and leverage it to assist you with any questions you have getting your VPS setup or configured.
Tmux - Shell Persistence

I’m not going to get into the weeds of what tmux is (cheatsheet), I’m going to focus on why it should be important to you. Tmux lets you have a persistent shell this means even if your internet drops you won’t lose all that progress or where your VPS shell was which is HUGE. Here is the tmux configuration I use:
#.tmux-conf
setw -g mouse on
set -sg escape-time 500
set -g terminal-overrides ',*:smcup@:rmcup@'Then you will want to use tmux to get a shell.
Now whenever you reconnect to your VPS simply use tmux -a to continue where you left off.
Here are some basic tmux hotkeys you will need to know:
All commands start with ctrl+b
c # Create new tab
n # Next tab
p # Previous tab
d # detach -- this does not end the tmux session it just detaches tmux -a reattaches
, # Rename current windowBringing it together
So now you have a VPS server setup that you can quickly connect to with ssh droplet you have a persistent shell with tmux. You have ax framework & claude code setup and configured.
I’ll be releasing a blog post on next steps, going over my current recon pipeline and tools I use often.